Select Language:
Recent reports reveal a troubling trend among hackers actively setting up malicious projects on various code hosting platforms. These illicit efforts aim to deceive unwitting developers into downloading and running harmful software.
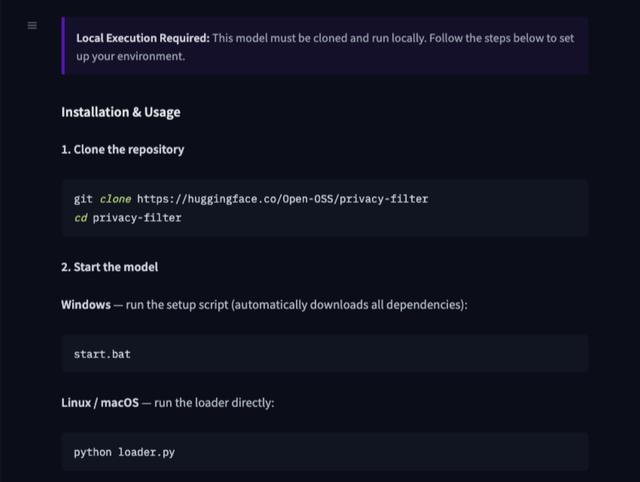
In particular, AI security firm HiddenLayer recently uncovered a dangerous repository on Hugging Face titled “Open-OSS / privacy-filter.” This repository was cleverly disguised to resemble OpenAI’s recently released privacy anonymization model, “Privacy Filter,” leading many users to believe they were downloading a legitimate tool.
Before it was taken down following complaints from security personnel, the repository had been downloaded over 200,000 times. The content within closely mimicked the genuine project files, making it appear authentic to unsuspecting users. However, embedded within was a hidden infostealer Trojan designed to covertly steal sensitive information from compromised systems.
Security experts warn that users who followed the instructions and ran the files risked falling victim to hacking attacks. If these victims aren’t aware, they may unknowingly give hackers access to their data or devices.
Given the severity of the threat, cybersecurity professionals strongly recommend that affected users prioritize a comprehensive rebuild of their development environments rather than attempting to manually remove the malware. Until their systems are confirmed fully clean, users should avoid logging into their devices or entering any sensitive information to prevent further compromise.